"It's us at the state level that can connect dots if things are happening in multiple jurisdictions in our state. " Federal officials say their goal is to sound the alarm louder and at higher levels of government than in past years, ensuring that information about efforts to interfere in the election reaches the state officials who need it the most and who have the best resources to deal with it. That is especially important since federal officials believe Russian agents in 2016 searched for vulnerabilities within election systems in all 50 states. Though the policy change means that a broader audience of government officials will learn of any intrusion, it does not guarantee that the American public will as well. FBI officials say they will continue to protect the privacy of individual hacking victims, including governmental offices or local elections systems, by not sharing their identities with the public. It will remain up to electoral officials to disclose if they've been hacked, or if they are working with the FBI.
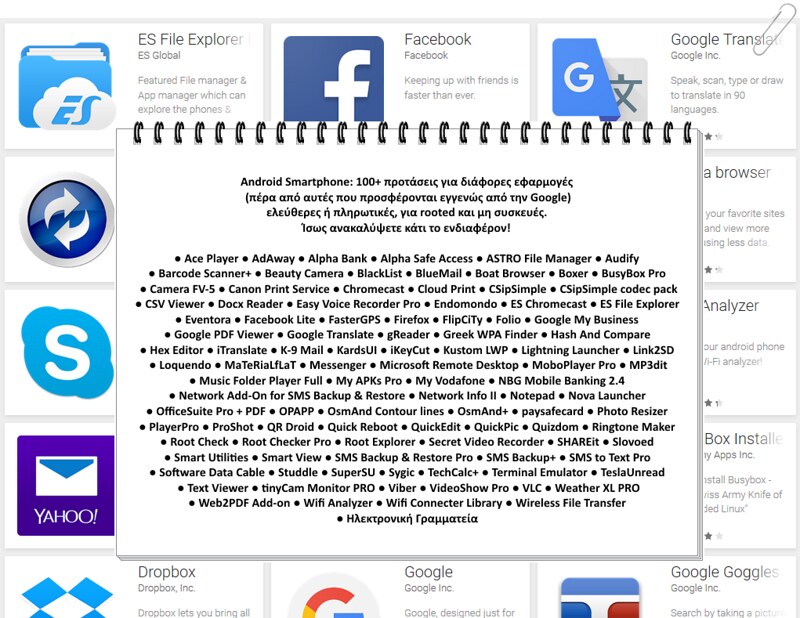
Wireless network analyzer free.fr http
There is also a notes tab to add custom text notes. WinFi Lite supports lots of filtering options to display a subset of networks or information only. You can sort the network table using the program and switch to another supported view mode using the view menu. The application supports basic and pro view modes, a security report view mode, or network capability and nearby network lists views. Basic, as the name suggests, lists fewer parameters and focuses on important metrics such as signal quality, band, or channel. Pro displays more information, and security report changes the layout of the table by grouping networks into security categories. It lists open networks and networks sorted into groups that use encryption for easier identification. You can create custom profiles using the program's capabilities; ideal if you need an overview of a subset of information only. A right-click on a network displays options to copy the information or save/open as Pcap., The developer added handy features to the application that improves how you use it.
Think of the progress that could be made with regards to treating certain kinds of diseases! " IBM's Eli Dow explained in a blog post. Dow added, "As you might appreciate, the concept generalizes to analytics and cloud storage for regulated industries in general. Basically most scenarios where information-sharing collides with the paradox of 'need-to-know' vs. 'need to share' would benefit from FHE. " The FHE toolkits are available on GitHub for macOS and iOS. Related: Microsoft Introduces Free Source Code Analyzer
Related: CISA Announces Open Source Post-Election Auditing Tool
Related: Google Releases Open Source Tool for Finding File Access Vulnerabilities
Eduard Kovacs ( @EduardKovacs) is a contributing editor at SecurityWeek. He worked as a high school IT teacher for two years before starting a career in journalism as Softpedia's security news reporter. Eduard holds a bachelor's degree in industrial informatics and a master's degree in computer techniques applied in electrical engineering.
The tech giant says the use of FHE is ideal for sensitive applications such as the ones used in the financial and healthcare sectors, allowing associated data to be shared without exposing it during processing. The open source toolkits released this week by IBM make it easier for developers to implement FHE. One practical use case suggested by IBM is for apps that allow users to search for certain types of products or services (e. g. restaurant apps). The use of FHE would allow the developer to implement what IBM describes as "privacy-preserving search, " enabling the user to obtain the information they are looking for without exposing the search query to the cloud provider. Another use case is for machine learning. Developers of machine learning systems could train their model using encrypted data provided by others analyzing the same type of problem, but without the actual data being made available. "For example, what if all the health care providers on the planet could pool fully encrypted patient records to allow analytics on patient data without divulging anything about the individuals involved.
Microsoft on Monday unveiled Project Freta, a free service that allows users to find rootkits and other sophisticated malware in operating system memory snapshots. Freta is the name of the street in Warsaw, Poland, where renowned scientist Marie Curie was born. The project's name is related to Marie Curie inventing a mobile x-ray device that could be taken to a battlefield. The Project Freta cloud-based service currently only supports Linux systems, but Microsoft plans on adding support for Windows as well. Project Freta aims to provide an agentless way for organizations to conduct automated forensic analysis on thousands of virtual machines in search of malware — ranging from cryptocurrency miners to rootkits — by looking at a captured image of volatile memory. The service leverages sensors that are designed to detect malware, but without tipping off the malicious software. According to Microsoft, the technology is built so that malware cannot detect the sensor before installing itself, malware cannot hide where it would not be seen by the sensor, the malware cannot detect operation of the sensor and take action to remove or change itself, and malware cannot modify the sensor to evade detection.
- Best small business cards
- Wireless network analyzer free software
- Many High-Risk Users Have Bad Security Habits: Google Survey | SecurityWeek.Com
In the case of a critical vulnerability affecting PostgreSQL, it was only added after 1, 817 days, which is the longest observed by RiskSense. Looking at the data for 2019, the company noticed that the number of CVEs was 968, a 130% increase compared to 2018, when there were 421 CVEs. However, only 15 of the security holes disclosed last year were weaponized. A total of 179 vulnerabilities were disclosed in the first three months of 2020, including five that have been weaponized. Overall, the highest percentage of vulnerabilities were described as information exposure, followed by cross-site scripting (XSS) and improper input validation issues. These last two categories had the highest number of weaponized flaws. "Some weaknesses were far less common, yet remained very popular in active attack campaigns, " RiskSense noted in its report. "Deserialization Issue (28 CVEs), Code Injection (16 CVEs), Error Handling Issues (2 CVEs), and Container Errors (1 CVE) were all seen trending in the wild.
Sophos this week removed the license check and activation requirements from Sandboxie, essentially making the isolation tool free. The move, the cybersecurity firm says, is the first step it makes toward releasing the sandbox-based isolation program open source. Initially developed by Ronen Tzur, Sandboxie was acquired by endpoint protection company Invincea in 2013. In February 2017, Sophos acquired Invincea, and Sandboxie became part of its portfolio. With a focus on securing endpoints, network, email, and mobile systems, as well as on providing unified threat management, Sophos never looked at Sandboxie as a significant component of its business. In fact, the company has been exploring options for its future for a while, and says that simply ending Sandboxie completely would have been the easiest and least costly decision. "However, we love the technology too much to see it fade away. More importantly, we love the Sandboxie community too much to do that. The Sandboxie user base represents some of the most passionate, forward thinking, and knowledgeable members of the security community and we didn't want to let you down, " the company explains.
When it comes to notifying states, one FBI official told the AP there was confusion in the past about who was receiving information and in what circumstances — issues the new policy is meant to address. The official said the policy is meant to ensure that one party does not hear it from the other before hearing it from the federal government. Related: Securing the 2020 Elections From Multifarious Threats
Related: New Election Systems Use Vulnerable Software
Related: Key Senate Panel Approves $250 Million for Election Security
Previous Columns by Associated Press:
High-risk users are aware that they are more likely to be targeted by hackers compared to the general population, but many of them still have bad security habits, a Google survey shows. High-risk user groups include business executives, politicians and their staff, activists, journalists and online influencers. Individuals in these categories are more likely to be targeted in cyberattacks due to their occupation or their online activities. Google has commissioned The Harris Poll to survey 500 high-risk users from the United States; 100 people from each of the five aforementioned categories. The results of the survey show that 78% of high-risk users are aware that they are more likely to be targeted by hackers compared to the general population, and 65% of them are more concerned about their accounts being hacked today than they were one year ago — a majority are mainly concerned about their work account being targeted. Nearly three-quarters of respondents have been targeted in a phishing attack and 39% admitted having their accounts compromised.
- Cricket scorebook software review
- Which of the following best defines e- commerce
- Crm email marketing.com
- Masters in psychology courses
- Auto load rates